Book contents
- Frontmatter
- Contents
- Foreword
- Preface
- 1 Introduction
- 2 Moving to Proactive Cyber Threat Intelligence
- 3 Understanding Darkweb Malicious Hacker Forums
- 4 Automatic Mining of Cyber Intelligence from the Darkweb
- 5 Analyzing Products and Vendors in Malicious Hacking Markets
- 6 Using Game Theory for Threat Intelligence
- 7 Application: Protecting Industrial Control Systems
- 8 Conclusion
- Glossary
- References
- Index
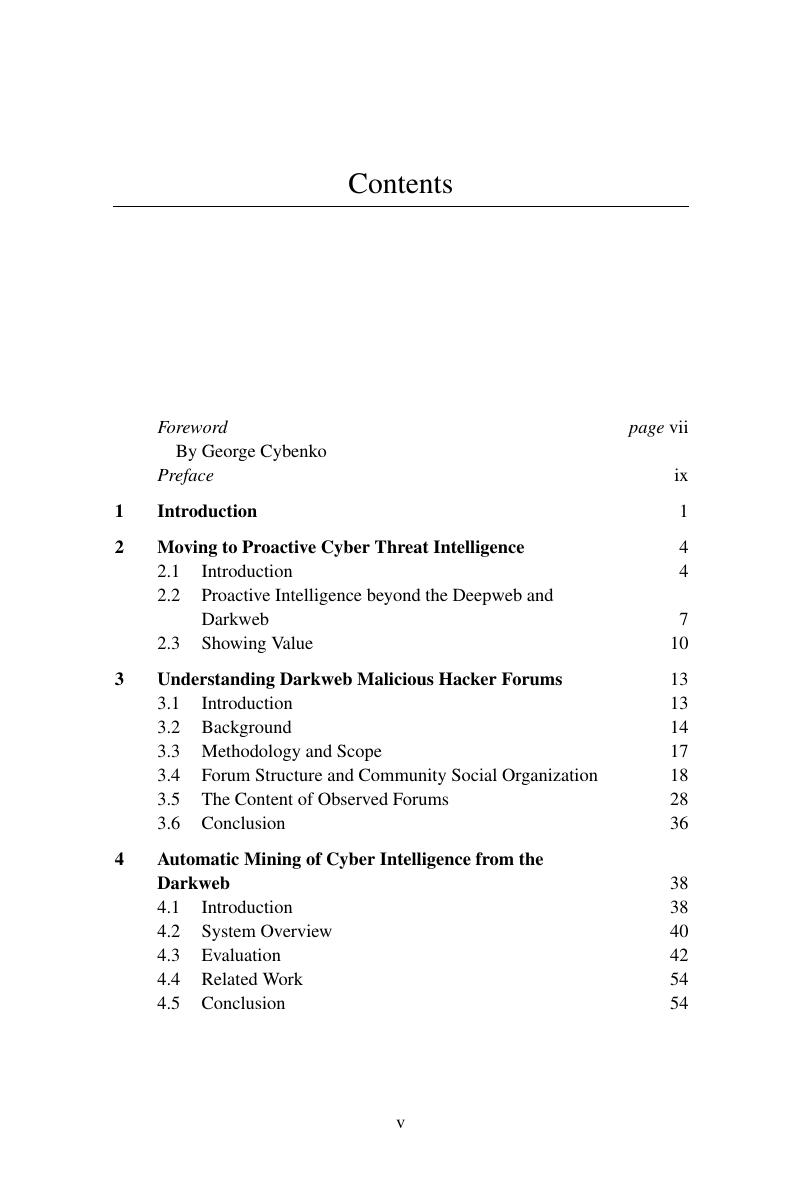
Contents
Published online by Cambridge University Press: 06 April 2017
- Frontmatter
- Contents
- Foreword
- Preface
- 1 Introduction
- 2 Moving to Proactive Cyber Threat Intelligence
- 3 Understanding Darkweb Malicious Hacker Forums
- 4 Automatic Mining of Cyber Intelligence from the Darkweb
- 5 Analyzing Products and Vendors in Malicious Hacking Markets
- 6 Using Game Theory for Threat Intelligence
- 7 Application: Protecting Industrial Control Systems
- 8 Conclusion
- Glossary
- References
- Index
Summary
- Type
- Chapter
- Information
- Darkweb Cyber Threat Intelligence Mining , pp. v - viPublisher: Cambridge University PressPrint publication year: 2017