Book contents
- Frontmatter
- Contents
- Preface
- Acknowledgments
- Artwork
- Notation
- Part I Introduction
- Part II Security games
- Part III Decision making for network security
- 6 Security risk-management
- 7 Resource allocation for security
- 8 Usability, trust, and privacy
- Part IV Security attack and intrusion detection
- A Optimization, game theory, and optimal and robust control
- References
- Index
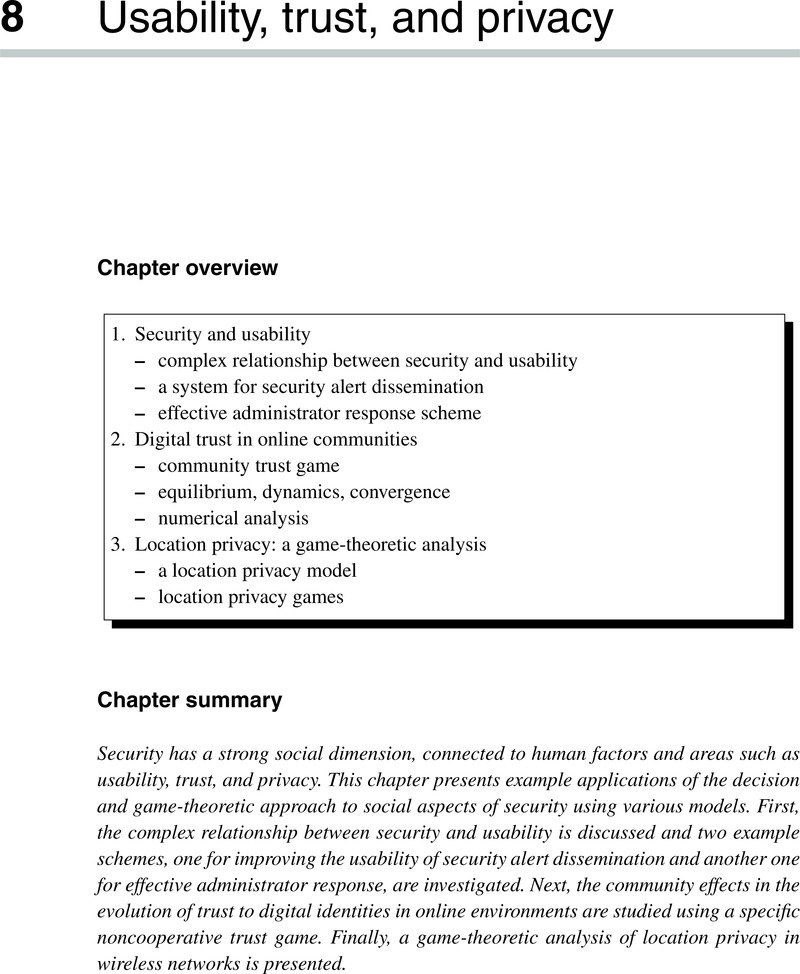
8 - Usability, trust, and privacy
from Part III - Decision making for network security
Published online by Cambridge University Press: 02 December 2010
- Frontmatter
- Contents
- Preface
- Acknowledgments
- Artwork
- Notation
- Part I Introduction
- Part II Security games
- Part III Decision making for network security
- 6 Security risk-management
- 7 Resource allocation for security
- 8 Usability, trust, and privacy
- Part IV Security attack and intrusion detection
- A Optimization, game theory, and optimal and robust control
- References
- Index
Summary
- Type
- Chapter
- Information
- Network SecurityA Decision and Game-Theoretic Approach, pp. 189 - 216Publisher: Cambridge University PressPrint publication year: 2010



